wifi-U lands in Aruba 🌐
 |
 |
 |

 |
 |
 |
To mesh, or not to mesh? And honestly, it’s a fair question. Mesh networks sound magical — simple, seamless coverage! But before you go mesh-crazy, let’s talk about what really happens behind the scenes.
Using the Wi-Fi Calculator, we ran a little experiment.
In the first picture you see that at 43.8 ft and using a U7Pro and a client with a Wi-Fi 7 card, we have an expected real-world speed of 310 Mbps. I can only achieve an MCS of 8 so I can’t take advantage of the high throughput speeds available with WiFi 7

When I add a U6 Mesh halfway between the devices I have a 430Mbps link between the Pro and the Mesh
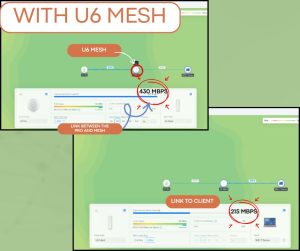
But only a 215Mbps link to the Client. What happened? Even though the Signal between the Mesh Device and the Client is excellent and I can achieve an MCS of 1,1 I still only get half the throughput that the Mesh Device is receiving.
⚠️ Welcome to the Law of Halves
Here’s the catch: Wi-Fi is half-duplex, meaning it can’t send and receive data at the same time. So when your Mesh AP talks to the main AP and your device, it’s splitting its attention — and its throughput.
Every time you add a mesh hop, your speed gets chopped in half:
And don’t even think about going beyond 4 — Ubiquiti won’t let you. The devices just won’t stay connected.
🛠️ So… Should You Mesh?
Here’s the golden rule: Mesh is great for small spaces with a few out-of-range clients — especially when running cable isn’t an option.
It’s installer-friendly, but user-unfriendly if you’re chasing high speeds or supporting lots of devices. If you can wire it, do it. If you can’t, mesh responsibly.
💡 Final Thoughts
Mesh networks are like fast food — convenient, but not always the healthiest choice for your network’s performance. Use them wisely, and your users will thank you.
Author: Eric Weber

wifi-U is excited to return to the Church IT Network this year as a Silver Partner!
The Church IT Network is a coalition of churches that meet both regionally and at an annual conference to discuss strategies and solutions to the IT challenges facing their ministries.
Last year, Eric and Ryan attended for the first time, and Ryan delivered a powerful presentation on using Unifi Protect to keep your church safe. This year, Ryan will be presenting “Let There Be Light…and Wi-Fi, and Cameras, and Door Access,” which will be bigger, better, and even more fun than last year’s presentation.
We’ll also have a booth with some Unifi demonstration equipment, and we’ll live-stream portions of the conference. If you’re in Cincinnati, be sure to swing by and say hello!
🚫 Don’t let your UniFi network stay stuck in “Automatic.” ✅ Take control with the right Ubiquiti training.
In our latest video our instructor, Ryan breaks down:
UWA, URSCA, UBWA, + wiFi‑U custom classes for pros and home users
To help YOU find the right class! Whether you’re an IT pro, WISP operator, small business owner, or just starting with UniFi at home — this guide will help you level up fast.
🎥 Watch now!
At wifi‑U, we’re all about helping you get the most out of your wireless networks. One feature that often flies under the radar but can make a big impact on performance is band steering. If you’ve ever wondered how your devices choose between 2.4 GHz and 5 GHz Wi-Fi bands — or why they sometimes seem stuck on the slower one — this post is for you.
Learn how it works, when to use it, and why it’s a must for modern networks. 📖 Check out our new Youtube Video Here!
Watch Our New YouTube Video with Wifi-u Instructor Ryan Haag!
In this video, Ryan from Wi-Fi U takes you inside his Unify Wireless Admin and Routing, Switching & Cybersecurity class in Lansing, MI. You’ll get an exclusive tour of the hands-on student setups featuring Wi-Fi 7 access points, UCG Ultra gateways, PoE switches, VLAN labs and OSPF routing exercises. Why Take a Hands-On Networking Class? Interactive labs accelerate learning and build confidence far beyond passive video tutorials. You’ll configure gear side by side with an experienced instructor, troubleshoot in real time, and leave the classroom ready to deploy unified network solutions in your environment. See why paying for live instructor-led training beats YouTube University every time.
Register now for upcoming Unifi Wireless Admin and Routing, Switching & Cybersecurity classes. Equip yourself with confidence to design, deploy, and secure enterprise Wi-Fi networks.

When it comes to smart security, simplicity often wins—and Ubiquiti’s SuperLink proves that point beautifully. This compact device, essentially a small box with an antenna, quietly solves a major problem: enabling long-distance connectivity for battery-powered sensors, especially in environments where Bluetooth falls short.
🛠️ Setup & Performance
I had the chance to test out a SuperLink early on. The initial setup had a bit of a hiccup in that all my originally adopted sensors would not migrate to the Superlink. After I reset and readopted them though, they popped right up. I decided to place some sensors outside while keeping the Superlink in my home. One sensor went on our pirate ship playhouse, another in our side yard, and the last one all the way out by the entrance to our driveway, over 150 feet away. Despite the freezing conditions, the sensors stayed reliably connected.
🚨 Big things are brewing at Ubiquiti this August—they’re teasing a wave of new sensors, and now’s the perfect time to grab a Superlink and get ahead of the curve. I believe the Superlink could mark a turning point, where everyday users start ditching costly ADT monitoring in favor of Unifi Protect’s push notifications to secure homes, rentals, and small businesses.
With extended-range sensors coming in August, we might even see Unifi gear expanding into agriculture and other underserved sectors that traditional security companies tend to overlook.
Bottom line? The Superlink has me genuinely excited about what’s next for Unifi Protect.
Author: Ryan Haag

Setting up VLANs with UniFi doesn’t have to be overwhelming. A recent Reddit thread sparked a great conversation between a Reddit user and our instructor, Ryan, on troubleshooting tips for VLAN setup. Check out the original post here: Reddit Post
In this post, we’ve pulled together the most useful advice in one place to create a clean, secure, and scalable VLAN architecture.
Stick to VLAN numbers like 20, 30, 40 instead of 2, 3, 4. This leaves room for expansion later (e.g., VLAN 21 for a test group within VLAN 20). It also makes port tagging and troubleshooting more intuitive when your VLAN IDs line up with your subnets.
Most users agree leaving management on VLAN 1. Changing it can lead to issues during adoption, firmware updates, or communication with UniFi cloud services.
Creating a dedicated IoT VLAN helps isolate smart devices from your main network, improving both security and performance.
Here’s what this looks like all put together:
VLAN 10: Management
VLAN 20: Main
VLAN 30: IoT
VLAN 40: Guest
VLAN 50: Voice or NVR
VLAN 60: Backup or automation
Each VLAN uses its own subnet (e.g., 10.10.20.0/24) and is segmented with strict firewall rules. DHCP reservations ensure consistency and make troubleshooting easier.
The UniFi ecosystem offers incredible VLAN flexibility — but it pays to follow best practices. Start small, plan your IP ranges, and test your firewall rules before going live.
Want to go deeper? Join one of our upcoming UniFi training sessions and learn hands-on how to build enterprise-grade networks the right way. Click here for training schedule.



Did you know Ubiquiti has solar products? Our instructors Ryan and Jason used a UISP Solar Point with some solar cells and batteries to power a remote camera system. The cameras connect to the Solar Point’s 4-port switch and use a UISP long range link to connect to the main UNVR at the site, allowing the customer to view and record nearby traffic.
Author: Eric Weber
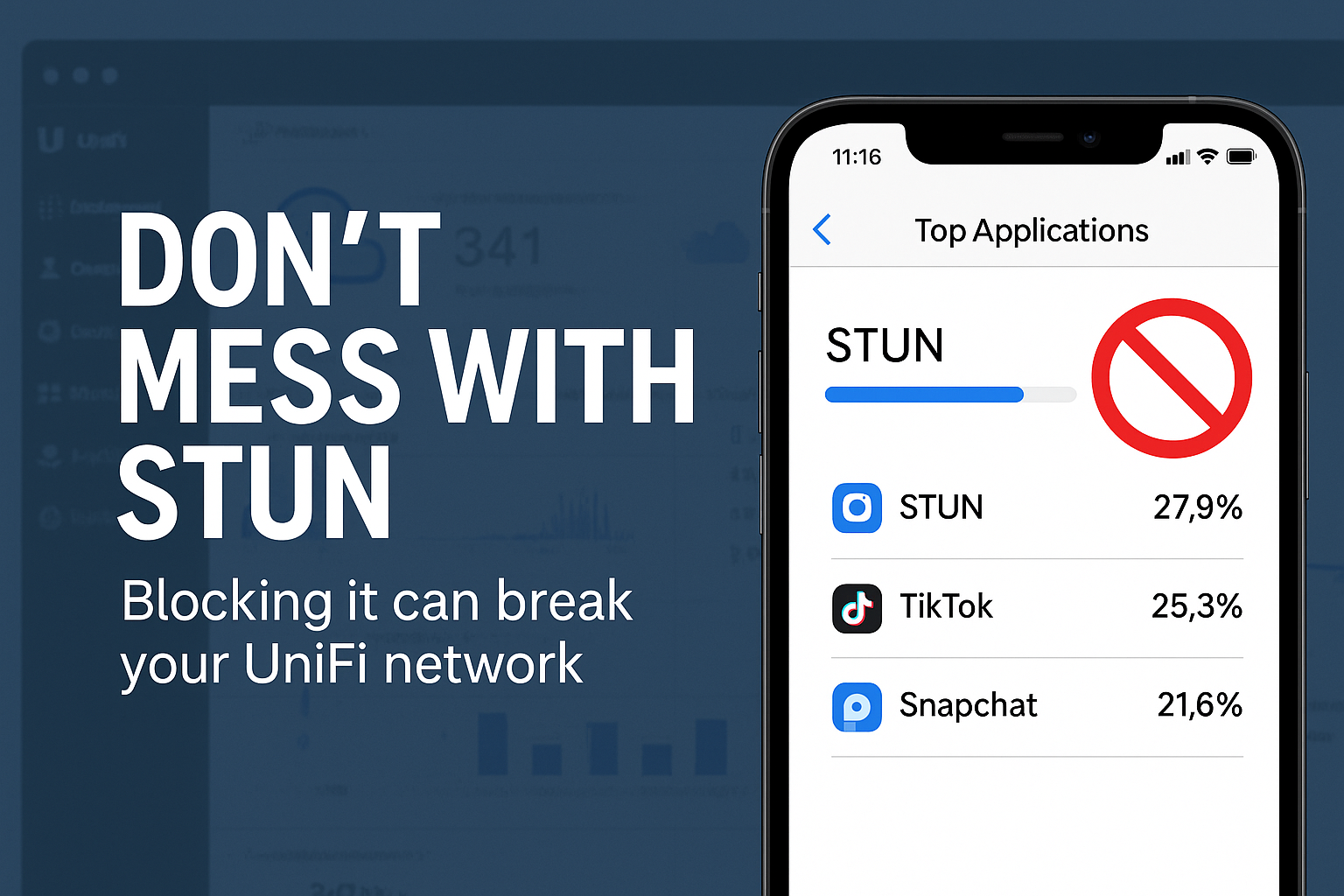
At WiFi-U, we love showing students how to take control of their networks. One of the powerful features in the UniFi ecosystem is the ability to block unwanted applications with just a few clicks. Whether it’s TikTok, Snapchat, or any other bandwidth-hogging app, UniFi lets you shut it down quickly and cleanly.
Imagine this, while scanning app traffic, STUN is showing up as one of your top bandwidth users. That might seem strange—especially on a quiet Wi-Fi network—but don’t panic. STUN isn’t doing anything malicious, and more importantly:
You absolutely should not block STUN.
STUN stands for Session Traversal Utilities for NAT, and it’s a vital part of how UniFi devices communicate with cloud services, especially when you’re running a self-hosted UniFi Network Application (e.g., on a Linux server).
If you block STUN traffic (usually using port 3478), your Access Points and Switches may not be able to reach the UniFi cloud infrastructure. That means:
❌ Your devices might not show up in Site Manager
❌ You may lose remote management functionality
❌ Troubleshooting will become much harder than it needs to be
In other words, blocking STUN can break your network visibility, which defeats the purpose of using UniFi’s management tools in the first place.
So next time you’re feeling like a network superhero and ready to kill off rogue apps—leave STUN alone. It’s one of the good guys. 👊
Want more hands-on training like this?
Check out our upcoming Ubiquiti courses and level up your network mastery: https://wifi-u.com/shop/
Author: Eric Weber